Decoding BONq DAO’s $120 Million Exploit | QuillAudits

Summary:
On February 1, 2023, BONq DAO was exploited with an oracle attack. The attackers completely changed the price of AllianceBlock’s $ALBT tokens via an oracle manipulation technique, which led to estimated losses of about $120 million.
BONq DAO:
Bonq is a non-custodial, decentralized, and over-collateralized lending platform that allows users to borrow against their own tokens. Users can access the liquidity of their own digital assets by locking them up in a trove, which is a smart contract controlled only by the users, and minting a low volatility payment coin, BEUR, pegged to the Euro.
The Bonq protocol is governed by the Bonq DAO. Governance decisions are made by the DAO directors, the DAO members, and BNQ token holders who stake BNQ.
For more on Bonq DAO, visit the official Docs.
Tellor:
Tellor is an immutable, decentralized Oracle protocol that incentivizes an open, permissionless network of data reporting and data validation, ensuring that data can be provided by anyone and checked by everyone. BONq DAO uses Tellor as their price oracle.
For more on Tellor, visit the official Docs.
Vulnerability Analysis & Impact:
On Chain Details:
Attacker’s Address: 0xcAcf2D28B2A5309e099f0C6e8C60Ec3dDf656642
Attacker’s Contract: 0xed596991ac5f1aa1858da66c67f7cfa76e54b5f1
TellorFlex Contract: 0x8f55D884CAD66B79e1a131f6bCB0e66f4fD84d5B
BONq DAO Contract: 0x4248fd3e2c055a02117eb13de4276170003ca295
Attack Txn: 0x31957ecc43774d19f54d9968e95c69c882468b46860f921668f2c55fadd51b19
2nd Attack Txn: 0xa02d0c3d16d6ee0e0b6a42c3cc91997c2b40c87d777136dedebe8ee0f47f32b1
The Attack Cause:
The root cause of the attack was that the BONq Protocol incorrectly integrated its WALBT / BEURtrove with the Tellor Oracle. It immediately consumes the latest data point reported to the TellorFlexOracle. Anybody can stake 10 TRB tokens and update the price of a token in the Tellor Oracle. The reporter has to risk losing their stake if they report bad data.
The Attack Steps:
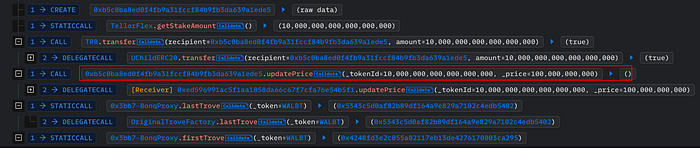
- The attacker first staked 10 TRB on the TellorFlex oracle, where they falsely quoted the price of WALBT tokens as 5000000 USD. He then and created a Trove transferred 0.1 WALBT tokens to the Trove.
2. The price was now extremely high as the BONq contract used the manipulated data from Oracle. As a result, the attacker borrowed $100M $BEUR tokens and used Uniswap to convert them into USDC.
He then created a second Trove of the WALBT asset and transferred 13.2 WALBT tokens to it.
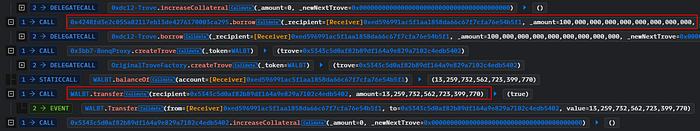
3. In the subsequent transaction, the attacker staked 10 TRB from a different address on TellorFlex once more, but this time he reported the price of WALBT tokens at 0.0000001 USD.
4. Then he liquidated multiple troves of WALBT tokens at a low token price, which he just updated.

5. Following the completion of both transactions, the attacker was ultimately successful in stealing 113.8 million WALBT tokens and 98 million BEUR tokens.
How could they prevent this attack?
The incorrect integration of the Tellor Oracle system, which consumed instant price feeds of the tokens, was the issue here. Price feeds should be used after a sufficient period has passed.
After the Exploit:
Bonq Protocol announced that they have paused the protocol and are currently working on a solution. They also released a community update on Mirror regarding this incident.
Status of Funds:
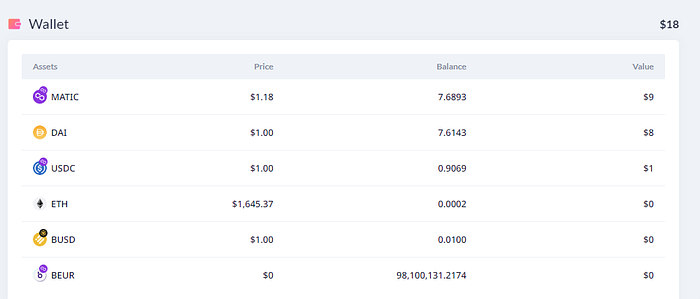
BEUR tokens were exchanged for stablecoins ($534K) and bridged to Ethereum along with 113.8m WALBT. On February 3, the attacker started moving the funds out through Tornado Cash.

At the time of writing this blog, the attacker currently has $18 left in his wallet.
Web3 security- Need of the hour
Why QuillAudits For Web3 Security?
QuillAudits is well-equipped with tools and expertise to provide cybersecurity solutions saving the loss of millions in funds.
Want more Such Security Blogs & Reports?
Connect with QuillAudits on :
Linkedin | Twitter | Website | Newsletter | Discord | Telegram
Partner with QuillAudits :
- Affiliate program ( Refer and secure web3 )
- QuillAudits Partnership Programme ( Venture funds, launchpads, development companies, marketing firms, web2 cybersecurity firms, web3 products )
- Join Ambassador program
