Decoding dForce Protocol “Read Only Reentrancy” Exploit | QuillAudits

Summary:
On February 10, dForce experienced an attack that resulted in a total loss of $3.64 million across both Optimism and Arbitrum Chain. It was a price manipulation attack due to the “Read-only Reentrancy” vulnerability. Around $1.73M was lost on Optimism and $1.91M on Arbitrum.
Introduction to dForce Protocol:
dForce promotes the development of a comprehensive suite of DeFi protocols for assets, lending, and trading, acting as the infrastructure for Web 3. It is currently deployed on Ethereum, Arbitrum, Optimism, Polygon, Binance Smart Chain (BSC), and KAVA.
Check out the official documentation for more information on dForce.
Vulnerability Analysis & Impact:
The Root Cause:
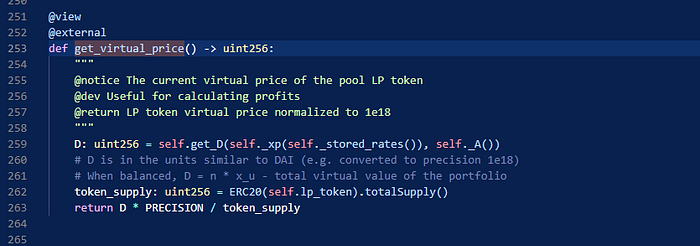
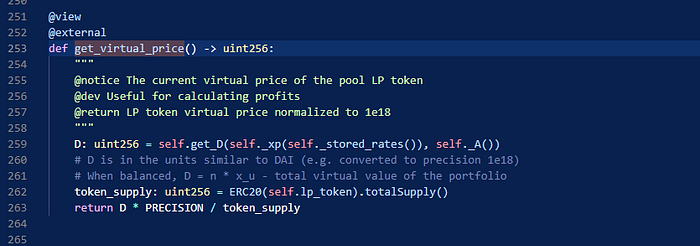
The attack was caused by Read-only Reentrancy in the get_virtual_price function of the Curve LP Oracle. The price oracle used by dForce’s lending protocol could be manipulated by the attacker. This enabled them to alter the price, reenter the function, and read the manipulated price to gain profit.
Read-Only Reentrancy:
The read-only reentrancy is a reentrancy scenario where a view the function is reentered, which in most cases is unguarded as it does not modify the contract’s state. However, if the state is inconsistent, wrong values could be reported. Check out this blog to learn more about this.
On-Chain Details:
Attacker Address: 0xe0D551017C0111aC11108641771897aA33b2817c
Attacker Contract: 0xee29b6aee6e4783db176946e4e8f1e5fdcd446a7
Attack Txn(Arbitrum): 0x5db5c2400ab56db697b3cc9aa02a05deab658e1438ce2f8692ca009cc45171dd
Attack Txn(Optimistic): 0x6c19762186c9f32c81eb2a79420fc7ad4485aa916cab37ec278b216757bfba0d
The Attack Flow:
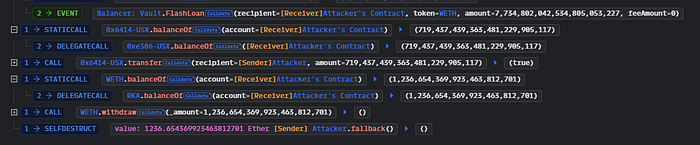
- The attacker took 68429 ETH from multiple protocols via Flash Loans.
2. Then he added liquidity to wstETHCRV, and received 65343 wstETHCRV in return. They then transferred 1,904 wstETHCRV to his other contract (0x53c5…7b28) and deposited it into the Vault via wstETHCRV-gauge, receiving around 1904 wstETHCRV-gauge.
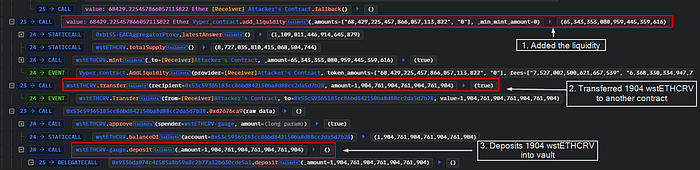
3. The attacker then invoked the remove_liquidity function to remove liquidity. When transferring ETH back to the attacker, the LP tokens were not burned, but the ETH pool was reduced.
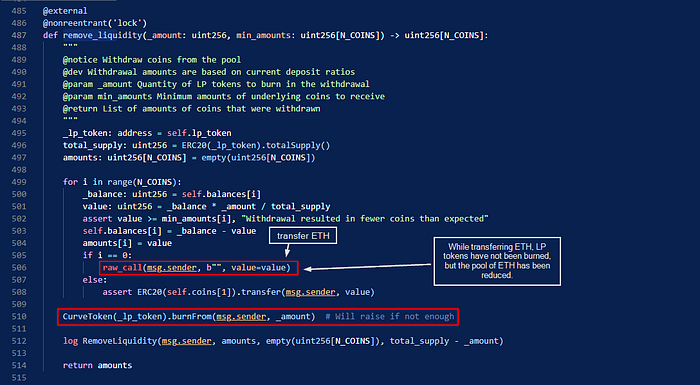
4. The get_virtual_price() function calculates the price using the total supply. Since ETH has been reduced and the total supply remains constant, this caused the virtual price to decrease.
As the oracle uses the virtual price of wsETH/ETH, the attacker manipulated the virtual price (using the above steps) and liquidated the position of other users in the vault. The attacker receives wstETHCRV-gauge tokens by doing so.
5. The attacker redeemed the $wstETHCRV-gauge tokens and received more tokens than before due to liquidation. Subsequently, He removed the liquidity, paid off the flash loan, and swapped $wstETH for $ETH. This resulted in a profit of 1236.65 WETH approximately $1.91 Million.

The attacker executed the same attack on Optimistic Chain and stole $1.73 million, making a total profit of around $3.6 Million.
After the Exploit :
On February 10, Immediately after the attack, the protocol paused all vaults and announced the hack via a Twitter thread.
On February 11, The dForce team negotiated with the exploiter to return the stolen funds, claiming to have identified the attacker’s IP, device information, and more. Additionally, they agreed to offer a bounty if the funds were returned. See here.
On February 13th, The hacker returned all the funds to dForce. In response, the dForce team agreed to offer a bounty and dropped all ongoing investigations and law enforcement actions. See here for more information.
Returned Amount:
Optimistic Chain — $1,671,81
Arbitrum Chain — $1,832,763
How they could have prevented the Exploit?
When interacting with the Curve LP protocol, particularly when obtaining a price, a reentrancy lock should be triggered before obtaining the price.
Web3 security- Need of the hour
Why QuillAudits For Web3 Security?
QuillAudits is well-equipped with tools and expertise to provide cybersecurity solutions saving the loss of millions in funds.
Want more Such Security Blogs & Reports?
Connect with QuillAudits on
Linkedin | Twitter | Website | Newsletter | Discord | Telegram
Partner with QuillAudits :
- Affiliate program ( Refer and secure web3 )
- QuillAudits Partnership Programme ( Venture funds, launchpads, development companies, marketing firms, web2 cybersecurity firms, web3 products )
- Join Ambassador program
