Decoding SwapX Protocol’s $1 Million Exploit | QuillAudits
Summary:
On February 27th, 2023, the SwapX Project was exploited on the BNB Chain due to a lack of access control. The attacker exploited the vulnerability to manipulate the price of the DND tokens, resulting in a total loss of $1 million of users' funds.
Vulnerability Analysis & Impact:
The Root Cause:
The contract was unverified, and after decompiling the code, we discovered that the victim contract does not implement proper access control in the 0x4f1f05bc function, making it simple for the attacker to transfer user tokens that had been approved for this contract.
On-Chain Details:
Attacker’s Address: 0x7d192fa3a48c307100c3e663050291fff786aa1f
Attacker’s Contract: 0xc4bea60f5644b20ebb4576e34d84854f9588a7e2
Victim Contract: 0x6d8981847eb3cc2234179d0f0e72f6b6b2421a01
Attack Transaction: 0x3ee23c1585474eaa4f976313cafbc09461abb781d263547c8397788c68a00160
Attack Process:
- The attacker first swapped around 0.0581 BNB for 1 Million DND tokens. See here:
2. Then the attacker repeatedly called the 0x4f1f05bc function of the victim's contract and exchanged other users' (who had approved the contract) BUSD for DND. This caused an inflation in the price of the DND token. See here.
3. Afterward, the attacker made a profit by swapping 1M DND for 739.6 WBNB. The attack was performed multiple times, resulting in a total profit of around $1 million.
And finally, the attacker self-destructed the attack contract.
After the Exploit :
At the time of writing this blog, there has been no official announcement from the team regarding the hack.
Status of the funds:
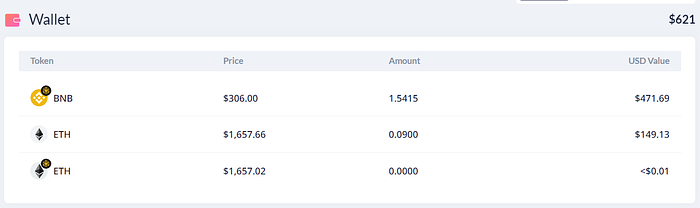
Attacker’s Wallet:
The attacker had about $621 in his wallet as of the date of this writing.
Reproducing the hack:
We will be using the Foundry framework for POC. For demonstration purposes, we will only drain funds from a few accounts.
Running Locally:
(Add the BNB Chain RPC URL in foundry.toml file and run the test using the command forge test -vvv)
How they could have prevented the Exploit?
This attack could have been prevented by implementing proper access control. Also, to prevent such attacks, it is important for users to periodically check and revoke access and permissions that have been granted. To revoke access, one can use revoke.cash.
Web3 security- Need of the hour
Why QuillAudits For Web3 Security?
QuillAudits is well-equipped with tools and expertise to provide cybersecurity solutions saving the loss of millions in funds.
Want more Such Security Blogs & Reports?
Connect with QuillAudits on :
Linkedin | Twitter | Website | Newsletter | Discord | Telegram
Partner with QuillAudits :
- Affiliate program ( Refer and secure web3 )
- QuillAudits Partnership Programme ( Venture funds, launchpads, development companies, marketing firms, web2 cybersecurity firms, web3 products )
- Join Ambassador program
