Decoding Thoreum Finance Exploit | QuillAudits
Summary:
On January 18, 2023, Thoreum Finance on BNB chain was exploited. The cause of the attack was a bug in the transfer function of the contract. The exploit caused the loss of approximately 2261 BNB ($680K) from the protocol. Then, the attacker used Tornado Cash to transfer the stolen money.
About Thoreum Protocol:
Thoreum is a liquidity mining protocol that offers static rewards to its token holders. Static rewards are automatically distributed to THOREUM holders. It is a hyper-deflationary token, which means that the supply keeps decreasing constantly with every transaction.
Check out the official docs to learn more about it.
The Root Cause:
The root cause of the attack was that during an upgrade of the contracts, the contract had a transfer bug. If someone called the transfer function to transfer tokens to itself, the tokens in the wallet would be increased by as much as the sent amount. Since the contract was not verified, we were unable to obtain more information regarding the actual codes.
On Chain Details:
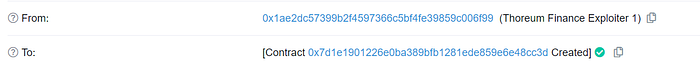
Attacker’s 1st Address: 0x1ae2dc57399b2f4597366c5bf4fe39859c006f99
Attacker’s 2nd Address: 0x1285fe345523f00ab1a66acd18d9e23d18d2e35c
Attacker’s Contract: 0x7d1e1901226e0ba389bfb1281ede859e6e48cc3d
Exploit txn: 0x5058c820fa0bb0daff2bd1b30151cf84c618dffe123546223b7089c8c2e18331
Contract Upgrade txn: 0x5a1788e1fbd582d1b89dc23fdf6cb7600c5ab07e4156b37cc3a6da27d5aa0349

Attack Steps:
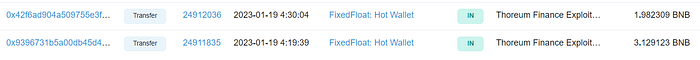
- The Exploiter first funded his wallet(0x1ae2d) from FixedFloat’s Hot Wallet and deployed his exploit contract.
2. The attack was very simple, The attacker simply deposited BNB to gain WBNB. Then he swapped the WBNB Tokens for THOREUM tokens on BiSwap.
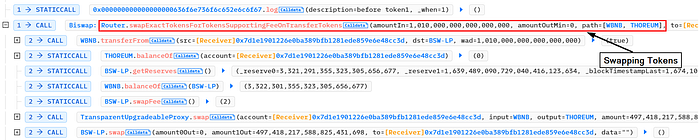
3. He called transfer function from the Thoreum contract and sent himself the tokens. He performed the transfer multiple times and due to the vulnerability his balance got increased each time.

4. The exploiter then converted all of the stolen tokens into BNB, amounting to approximately 2261 BNB.

After the Exploit:
Trade was temporarily suspended by the protocol. After a few hours, trading resumed as usual.
The protocol announced a Report of the incident through Twitter.
Status of the Funds:
The Attacker transferred 2250 BNB through the Tornado cash.
The attacker had $15 left in his wallet as of the time of writing this blog.
How could this incident have been avoided?
Security is one of the important aspects of web3, considering the recent turns of events in Defi and web3 where the code is money as well as law.
They should have conducted multiple audits by Reputable firms to ensure the security of the contract and that all potential vulnerabilities are discovered and resolved before deployment.
QuillAudits is well-equipped with tools and expertise to provide cybersecurity solutions saving the loss of millions in funds.

Web3 security- Need of the hour
Why QuillAudits For Web3 Security?
QuillAudits is well-equipped with tools and expertise to provide cybersecurity solutions saving the loss of millions in funds.
Want more Such Security Blogs & Reports?
Connect with QuillAudits on :
Linkedin | Twitter | Website | Newsletter | Discord | Telegram
Partner with QuillAudits :
- Affiliate program ( Refer and secure web3 )
- QuillAudits Partnership Programme ( Venture funds, launchpads, development companies, marketing firms, web2 cybersecurity firms, web3 products )
- Join Ambassador program
