How Did Zoth lose $8.4M due to Access Control
Incident Summary
On March 21, 2025, at 08:47:35 AM UTC, the Zoth protocol suffered an exploit due to a compromise of its deployer wallet, which led to the unauthorized upgrade of a proxy contract to a malicious implementation.
This allowed the attacker to withdraw approximately $8.4 million USD0++ tokens, which were quickly swapped for DAI and later converted into ETH.
The attack appears to have been planned weeks in advance, with all associated accounts being funded via ChangeNOW.
Timeline of Events
Initial Funding & Preparation
March 14, 2025, 12:49:47 PM UTC:
Attacker’s wallet 0x3b33c5cd948be5863b72cb3d6e9c0b36e67d01e5 was funded with 0.54626537 ETH (~$1,072.12) via ChangeNOW.
March 15, 2025, 04:58:35 PM UTC:
Attacker deployed a malicious contract at 0xc89d7894341e13d5067d003af5346b257d861f56.
Execution of the Exploit
March 21, 2025, 08:47:35 AM UTC:
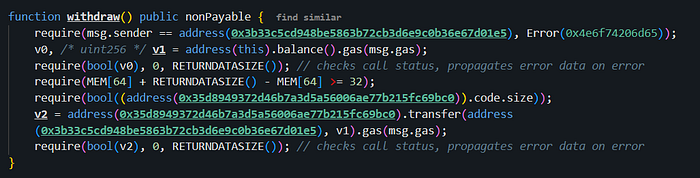
The attacker, having compromised the Zoth deployer wallet, upgraded the USD0PPSubVaultUpgradeable proxy contract to the malicious implementation.
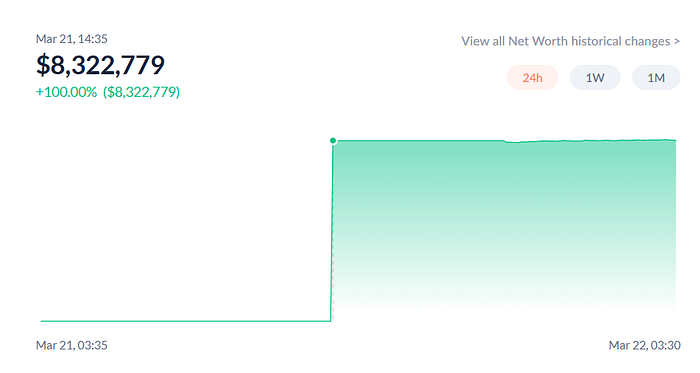
The attacker executed transaction 0x33bf669d125d11c432ac9b52b9d56161101c072fd8b0ac2aa390f5760fb50ca4, withdrawing 8,851,750.373778311459263 USD0++ tokens (~$8,484,544.36) to address 0x3b33c5Cd948Be5863b72cB3D6e9C0b36E67d01E5.
Immediately after:
- The attacker swapped USD0++ tokens for 8,323,591.477168 DAI (~$8,319,354.77).
- At 09:06:47 AM UTC, the attacker sent the 8,323,591.477168 DAI to their second wallet 0x7b0cd0d83565adbb57585d0265b7d15d6d9f60cf.
- Using CoW Swap and Uniswap V2, the attacker swapped the entire DAI balance into ETH via transaction 0xef528f68bf9ed5e8b3d502435d4773fb70d4d682c8a019e20b6818692ade5dc3.

The attacker currently holds all funds in ETH in their second wallet 0x7b0cd0d83565adbb57585d0265b7d15d6d9f60cf.
Failed Pre-Exploit Attempt
March 20, 2025 (20 hours before the exploit):
- The attacker attempted to upgrade the proxy contract to the malicious implementation but failed.
- Failed transaction: 0xeb87081cfb61a5ec8ebab8a4e9e4734af51cdd2317c43c6c96e58394870f2b1f.

Root Cause Analysis
The exploit was made possible due to a compromise of the deployer wallet, which had admin privileges over the proxy contract.
The attacker gained access to this Externally Owned Account (EOA) and used it to execute an upgrade to a malicious implementation contract, granting them complete control over funds.
Key Findings
- Admin Privileges Leak: The deployer wallet, which had direct control over the proxy contract, was compromised.
- Malicious Implementation Deployed: The attacker deployed a contract (0xc89d7894341e13d5067d003af5346b257d861f56) designed to exfiltrate funds.
Well-Planned Attack:
- The attacker funded their account 7 days prior via ChangeNOW.
- Multiple transactions suggest they tested their approach before executing the attack.
- They attempted the contract upgrade 20 hours before the exploit, indicating trial-and-error before success.
Recommendations & Mitigation Strategies
- The deployer wallet being an EOA created a single point of failure. Future upgrades should require multisig approval (e.g., Gnosis Safe).
- Consider using time-locked upgrades with community or third-party oversight to prevent instant malicious changes.
- Use hardware wallets or MPC (multi-party computation) to safeguard admin keys.
- Conduct internal security audits on key management practices.
- Implement on-chain monitoring alerts for administrative actions, such as contract upgrades.
- Introduce role-based access control (RBAC) to limit the scope of admin privileges.
